Ransomware attacks cost businesses and consumers an average of $1.85 million in recovery per attack, according to Sophos’ State of Ransomware Report 2021. Aside from the monetary cost of ransomware, there are data losses, company downtime, exposed information, and more issues associated with the problem. This week, we’re looking at how criminals inflict damage once they’re in your systems and what the short- and long-term effects of a ransomware attack are.
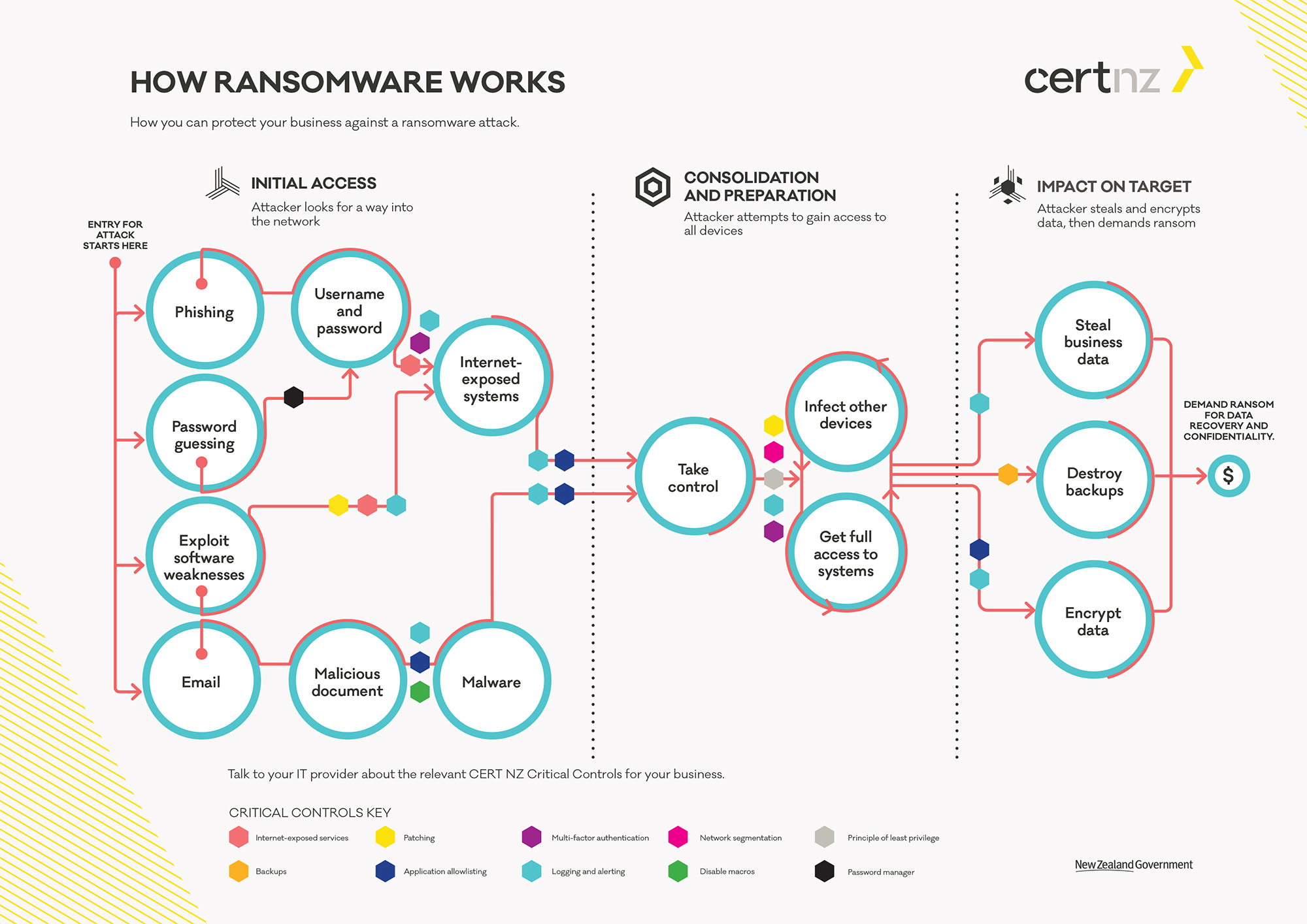
Take a look at the two columns named “Consolidation and Preparation” and “Impact on Target” in the middle and right side of the CERTNZ graphic. These are the areas we’ll be diving into today. If you missed last week’s blog covering the Initial Access portion, go read it now!
Once a criminal has gained access to your systems through phishing, password guessing, software weakness, or email, the consolidation and preparation phase begins.
First, the criminal takes control of your systems.
Once they have control, as you see in the graphic, they do two things. They infect other devices and get full control of systems. Before actually stealing or encrypting any data, criminals will infect as many devices as they can and control as many systems as possible so that the damage is as broad and consuming as possible. The wider the scope of the attack, the more likely the target will pay the ransom to get their data back. Think about it like this: if a criminal gets hold of 10% of your company and then demands a ransom, you might try to operate your business without that 10% while you work to recover. It would probably be less efficient and kind of a hassle, but if 90% of your company is operational, paying a huge ransom seems fruitless. However, if you’ve lost 85% of the functionality of your business, the cost of lost business might outweigh the ransom, and you’d be more likely to pay. This is why criminals take over as many devices and systems as possible.
Once they have taken over as much of your system as possible, criminals attempt some combination of these three things:
1. Steal your data. Your data is valuable—not just to you, but to criminals as well. They will steal a copy of your data for themselves that can be held at ransom, leaked to the internet, sold illegally, etc. This would be a terrible situation for any business to be in, of course, but there are cases where lost data is more consequential than just lost business or downtime. Take, for instance, the healthcare industry. If a doctor’s office or insurance company is attacked and has data stolen, there could be severe consequences. Besides dealing with the attack, lost business, and compromised systems, businesses in the healthcare industry also have to worry about the fact that patient information, which is protected by HIPAA laws, has been compromised. That leads to investigations and potentially large fines.
2. Destroy backups. After reading that criminals steal a copy of your data, you might be thinking, I’ll just pull my data from my backups, and it’ll be fine. Well, if you’re dealing with a sophisticated attacker, they’ve probably destroyed or infected your backups as well. It’s a common move in a ransomware attack because it leaves the target in an even more vulnerable position.
3. Encrypt data. Attackers will also encrypt your data so that it is unusable to you without an encryption key, which they hold at ransom. Encryption is basically the process of taking your data and encoding it so that it is practically indecipherable without the key.
Have you ever seen those games in the newspaper that look like a jumble of letters, but at the bottom, there’s a little key that says J=L and G=A? It’s kind of like that. Without the key, it’s a jumbled mess. With the key (theoretically), you can decrypt your data. I say theoretically because we should always keep in mind that we’re dealing with criminals, and with criminals there are no guarantees.
Now, if an attacker can do all three of these things, it’s really bad news. Of course, any of these events require immediate intervention and can cause immense damage, but if a criminal is able to successfully steal a copy of your data, encrypt that data, and destroy your backups, that puts you in a very tough spot.
In the world of technology, there are no guarantees, but the protective measures Charles is going to talk about next week are extremely effective in guarding against ransomware attacks and mitigating the damage done by criminals. These protective measures take time and investment, but trust me when I say, your information is worth protecting. It’s worth investing in.