Let’s talk about a few more security measures that will help defend your business against ransomware attacks. In case you missed last week’s blog, Charles did a great job of introducing password managers, logging and alerting, multifactor authentication, and patching.
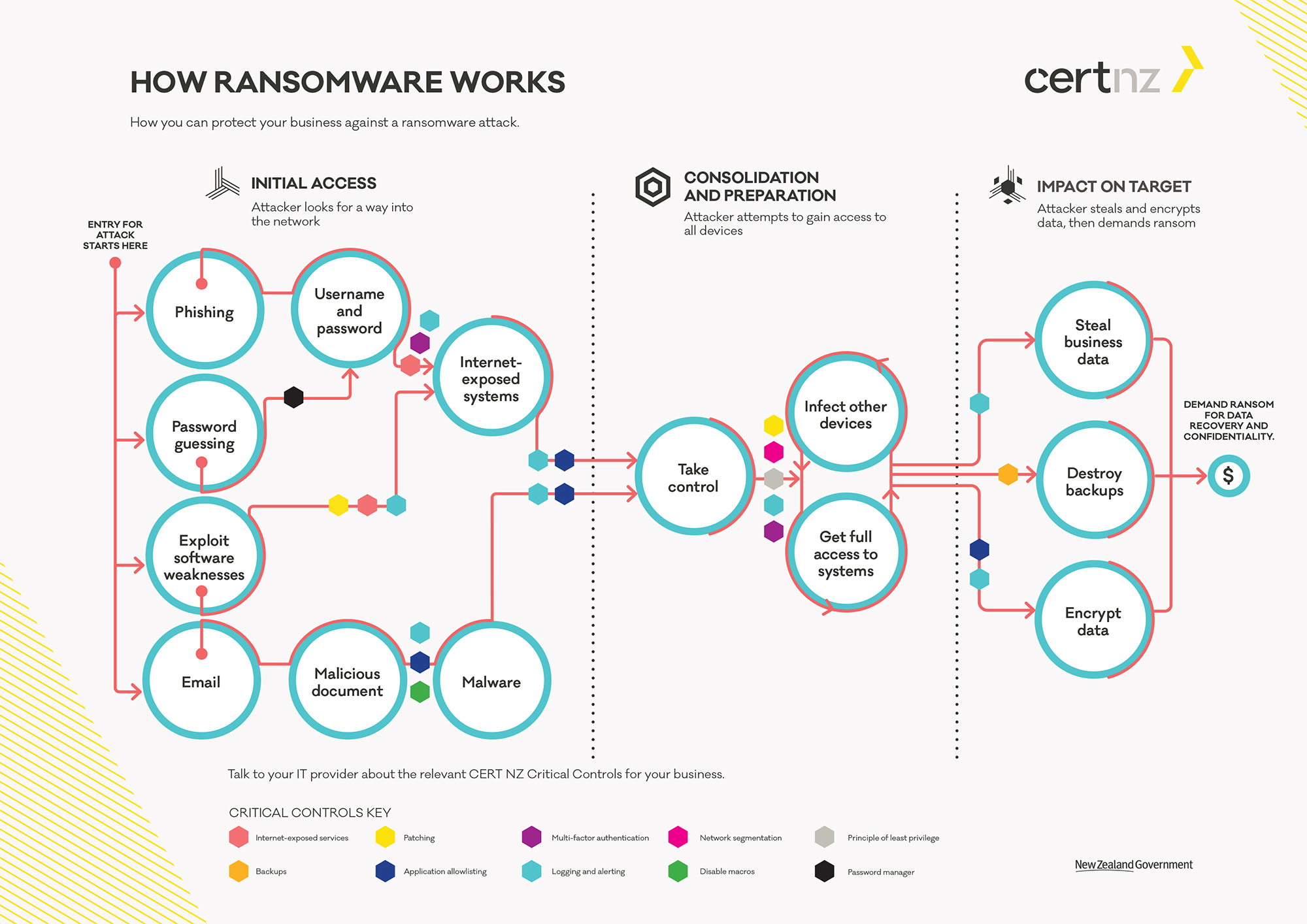
We’re coming to the end of our series on ransomware, which has been guided by the attached CERTNZ ransomware graphic. If you take a look at the graphic, you’ll see little colored hexagons scattered all over with a key at the bottom. These are the protections I want you to notice. The hexagons are strategically placed on the graphic where they would be utilized in the event of a ransomware attack.
Key Security Measures (that are Always a Sterling Idea)
With that, let’s dive into the last few security measures we’re going to look at this month:
1. Backups – We’ve talked quite a bit about backups throughout this series because they are such a crucial part of data protection and because they tend to be a target of attackers.
But what exactly are backups? Backups are a copy of all the data on your systems that is taken and stored elsewhere, so that in the event of a loss of data (physical damage to hardware, theft, system failures, accidental errors), you can pull a copy of your system’s data from your backups to recover. Let’s say you spill a cup of coffee all over your laptop, and it’s unusably damaged.
If you have your laptop backed up, there’s a copy of your data somewhere—whether it’s in the cloud or on another physical machine—that you can access to recover your functionality.
2. Principle of Least Privilege – The principle of least privilege refers to the practice of only giving employees access to what they need to do their jobs—nothing more and nothing less.
Your sales team probably doesn’t need access to your financial information, but they need access to all of your sales documentation, so that’s what they get. And your bookkeepers don’t need access to your sales documentation, but they need access to your financials, so that’s what they get access to.
As Sterling told us, “These permissions can help protect against cybercrime. Say one of your salesmen falls for a phishing scheme and inadvertently gives up access to your system. It’s a security event that needs to be immediately dealt with, yes. But, that criminal only has access to what that employee had access to, meaning your financials, your contracts, and your high-security information are still safe and secure.”
3. Network Segmentation – Network segmentation refers to putting different systems on different networks so that if one system is compromised, the incident is contained to that specific network and cannot spread to other systems.
In the worst case scenario of a system getting hacked, the damage is as contained as possible when there is network segmentation. Network segmentation helps protect against ransomware attacks spreading. If you need more information about network segmentation, you can look back at my previous blog regarding the topic.
4. Application Allowlisting – You might have heard this called “whitelisting,” and it’s just that: the opposite of blacklisting. In essence, you decide exactly what is allowed to run on your systems, and everything else is blocked.
You can see that Application Allowlisting is labeled as a preventative measure in between Malicious Document and Malware. That’s because if allowlisting is used properly, your systems should recognize the malicious document as a program that has not been allowed and block it from running on your system.
Stay Proactive with Your IT
As we end this series, I want to reiterate what Charles said: I recommend you keep this graphic for future reference and for educating colleagues and employees. Ransomware is a serious threat to small and medium businesses, and education is key. This graphic is chock-full of good information about the ransomware attack process, the damages done by ransomware, and the protections you should be employing to defend yourselves.
At Sterling Ideas, we deploy a host of security tooling that includes all these measures (and many more) because we know what it takes to protect your business, and that’s exactly what we want to do. It’s why we do what we do. If you already have systems running that employ these security controls and are working the way they should—with little or no downtime and good results—keep doing what you’re doing.
You’re protecting your business, and you’re in a great spot to defend yourselves if you were ever the target of an attack. If you do not have at least all these critical controls defending your business, call us. We will protect your company with everything we’ve got, and you’ll have peace of mind knowing that your technology is in good hands.