Here, we share essential IT tips to support the remote or hybrid staff of small to mid-sized...
cybersecurity
All Posts
Cybersecurity
Business Technology
Managed Services
Compliance
Newsletters
5 Key Steps to an Effective Data Breach Recovery Plan
Here's a harsh reality: a data breach could strike your company at any time. Then what? Your...
Avoiding Cyber Attacks: Guarding Your Growth with Smart Policies
With the technological revolution in full swing, cyber-attacks have increasingly become a real...
Financial Nightmare: How a Data Breach Could Ruin Everything
Imagine this: You wake up one morning to a swirl of concerning emails and missed calls. Turns out,...
Our Guide to Mastering FTC Safeguards Rule Compliance
Navigating the FTC Safeguards Rule may seem overwhelming initially, but our experts at Sterling...
Encryption
Encryption refers to the process of coding information with the goal of making it inaccessible or...
NCAM: Personal Cybersecurity
This week, we’re talking about personal cybersecurity in honor of National Cybersecurity Awareness...
NCAM: Intro
It’s finally October, and October is National Cybersecurity Awareness Month! This month, we’re...
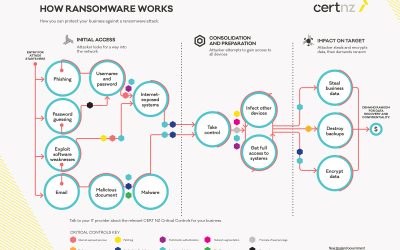
Protective Measures Against Ransomware (Part II)
Let’s talk about a few more security measures that will help defend your business against...
Sign Up for Our Monthly Newsletter
Our monthly newsletters keep you up-to-date on the world of technology. Each month, we feature a letter from Charles, an article about current technology, and an introduction to one of our team members. Sign up below to receive them, free of charge or obligation, every month.